Imagine a world in which people are completely reliant on a Super-Machine for all their needs…
Living in self-contained areas, they have little social contact, but are content because they’re sheltered and warm, with access to food, communication and entertainment – all enabled by the Machine. But one day the Machine goes down, and society crashes into a new reality. Does it sound… plausible? This is actually the plot of a science-fiction book written by EM Forster, called ‘The Machine Stops’.
In the real world, when people ‘sheltered in place’ during the Covid-19 pandemic, South Africans embraced online communication, shopping, banking, remote working and entertainment like never before – and when the pandemic eased, many people didn’t particularly want to go back ‘outside’ in quite the same way.
So even though we aren’t living in the sci-fi world of ‘the Machine’, the question is: How reliant are people today on the Internet? And has modern Internet usage made us more vulnerable to previously unimagined threats? The answers might be a bit shocking.
The Power’s Out
Let’s start with one of the basics: electricity. In South Africa, we’re used to power outages. Over time, we’ve come up with multiple solutions to deal with challenges like no heating or lights, cooking on gas instead of electricity, and having the Wi-Fi go down. But that was all because of Eskom’s troubles, which (whisper so as not to jinx things) might be on the mend at last?
Much more alarmingly, there are places in the world where the power can be taken out by acts of war, because the rise of technology means infrastructure is now linked to the online world. This brings improved functionality to critical national infrastructure sites around the world, but also new vulnerabilities – including electricity grids.
For example, Ukraine has experienced documented cases of cyber attacks on its power grid that have been attributed to its Russian enemies, in addition to actual physical attacks via traditional weapons of war.
The reality is that the Internet is now so intricately involved with our critical infrastructure that power outages – which can be life threatening in some situations – can be caused by online activity as well as physical damage. So yes – modern Internet usage has definitely made us more valuable to this particular threat.
The Internet of Threats
On a smaller scale than targeting national infrastructure, there are other ways in which the Internet can cause us to be vulnerable in our daily lives.
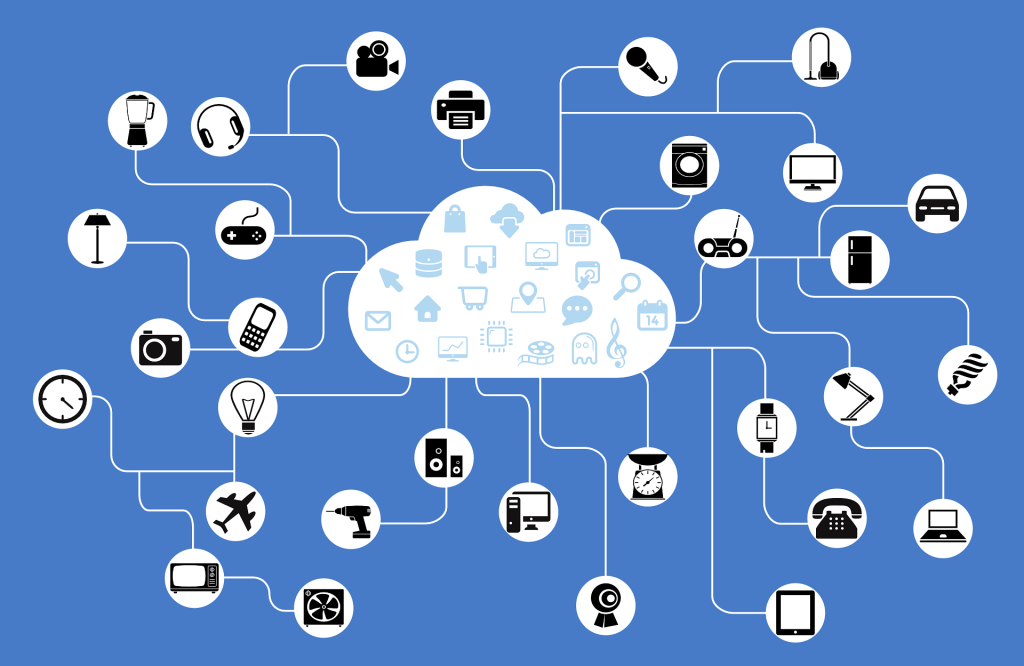
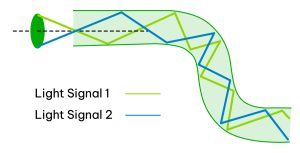
We’re used to connecting different devices to the Internet, including industrial sensors and CCTV cameras, as well as home devices such as security cameras (again), Internet routers, smart utility meters, connected TVs, and monitors for our small children’s bedrooms. Together, they form part of the Internet of Things (IoT), geared to make life easier.
However, many of these devices are set up with a default password already installed -that is something as basic as ‘Password’ – with the onus on the owner or installer of the IoT device to change it once in use. But frequently, the password isn’t changed – and in addition, there are lists of widely available (if you know where to look) IoT device passwords available on the Internet for threat actors to access quite easily.
The danger of IoT devices being hacked includes strangers spying on your home and frightening your kids through the baby monitor (yes, this really has been done), as well as, at a more industrial level, being turned into ‘zombie bots’. The so-called zombies become part of a botnet – a network of private computers or IoT devices infected with malicious software, and controlled as a group (without the individual owners’ knowledge) to carry out cyber crimes.
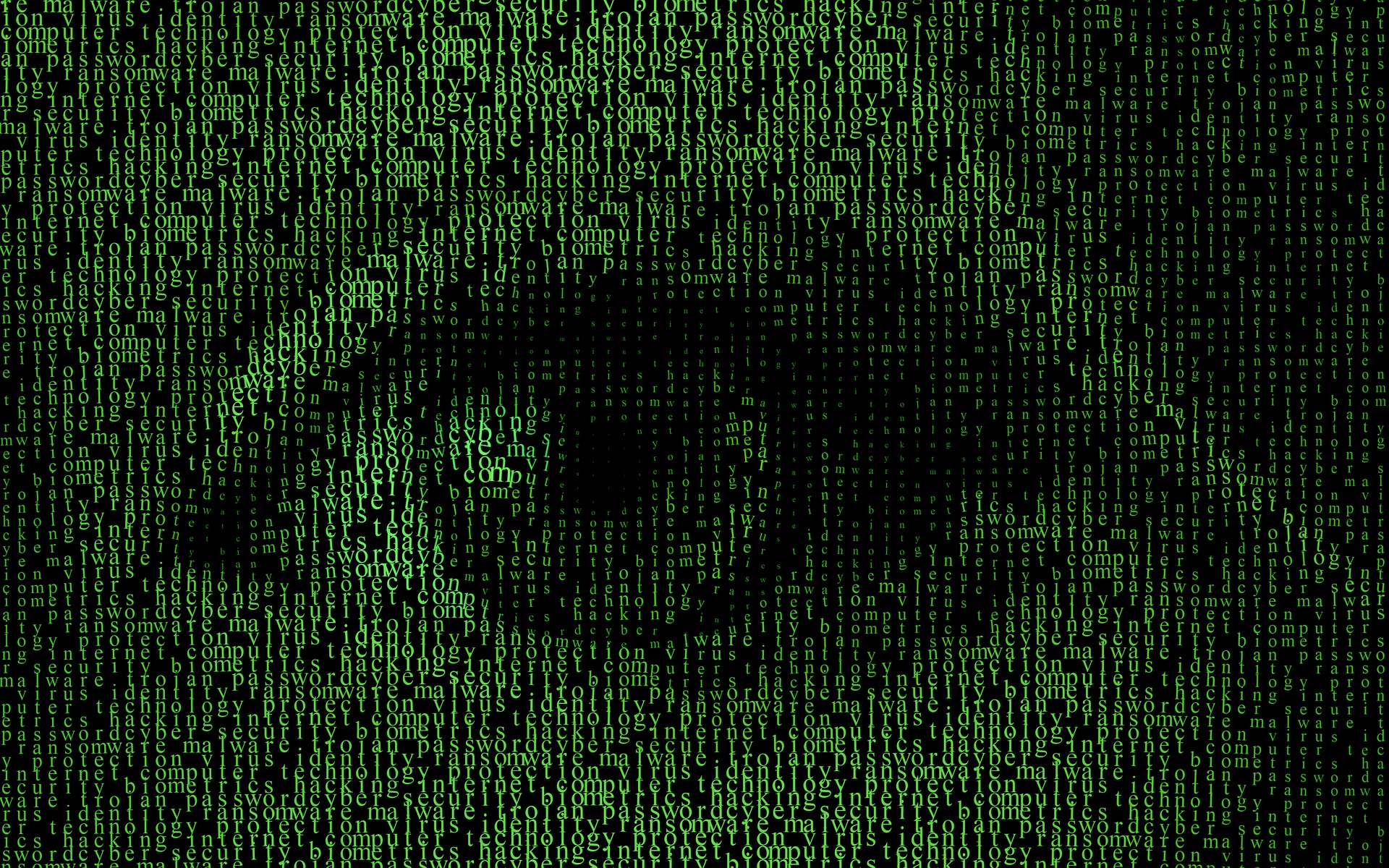
In late May 2024, the US Federal Bureau of Investigation (FBI) carried out an operation to take down what was thought to have been the world’s biggest-ever botnet, made up of millions of computers, in nearly 200 countries, that had been infected with malware. Selling access to this network enabled serious crimes around the globe, including financial fraud, identity theft and bomb threats.
It sounds like something from the movies, but unfortunately it’s not – it’s a reality today of modern Internet usage. So how do people and countries protect themselves from such possible cyber threats?
Protecting Your Data and Yourself
There’s obviously not a great deal that individuals can do to protect national infrastructure – that’s up to the sovereign nations concerned. As far as IoT devices are concerned, hopefully manufacturers, service providers and security experts are becoming more invested in developing effective strategies to improve their security – but it’s imperative that the consumer also shares the responsibility.
Here are some tips to make yourself less vulnerable to Internet threats:
- For any device in your home: change the default password to something stronger.
- Ensure that you have a strong Wi-Fi password for your home network.
- Install all updates from the manufacturer to ensure you have the latest security patches.
- Install, and then continue to update, anti-virus and malware software on your computers.
We are definitely more connected today than ever before – even if not actually within an all-powerful Machine – but at the same time, we have also become more vulnerable to threats from the Internet. Terrorists and criminals have shown their ability – and unfortunately their willingness – to use technology to harm countries, organisations and individuals. The reality is that no one is immune.
Here at Vox, we understand the vulnerability that comes with modern Internet usage. The only way to stop cyber criminals from making use of ‘the Machine’ in ways that unleash harm is to be constantly more aware and proactive.