Vox partnered with the South African Heritage Resources Agency (SAHRA) to deliver an integrated programme of connectivity, voice and network security, demonstrating how SAHRA connectivity and SD‑WAN for heritage sites can safeguard archives, improve communication and reduce costs. SAHRA requires a modern, secure and resilient IT environment to protect national heritage records and support remote working.
Planning SAHRA’s Connectivity and SD-WAN for SA’s Heritage Sites
The South African Heritage Resources Agency (SAHRA) is an agency of the Department of Sport, Arts and Culture – formerly known until 2000 as the National Monuments Council – which is tasked with an overall legislative mandate to identify, assess, manage, protect and promote heritage resources in South Africa, and to protect them for future generations.
National heritage sites need to be protected and safeguarded from damage or alteration, and it’s important to prevent development that could endanger their existence. As a national agency with additional provincial authorities, SAHRA works with local communities to identify heritage resources and record their oral and living histories, as well as increase public involvement in the preservation of heritage resources.
“South Africa has a very rich heritage,” says Stephen Muller, SAHRA ICT Manager, “and SAHRA works across a number of business units – including Heritage Properties, Burial Grounds and Graves, the Built Environment and Heritage Protection – to identify and protect heritage resources in South Africa.
“We have a very valuable registry in the form of our internal archives, encompassing a vast amount of heritage documents including old papers, plans, maps, information about graves…. information from the past that it’s important to protect and preserve.
“Overall, our outlook for the future is to become significantly more digitalised, including with our registry and archives, and also as an organisation overall. The work done by SAHRA is valuable and it’s important that it’s assisted in the digital realm, to protect South Africa’s Heritage Sites in the physical realm.”
South Africa has eight World Heritage Sites, as follows: Robben Island (Western Cape), iSimangaliso Wetland Park (formerly known as the Greater St Lucia Wetland Park in Kwa-Zulu/Natal); the Cradle of Humankind (Gauteng), Maloti Drakensberg Park (Kwa-Zulu/Natal), Mapungubwe Heritage Site (in Limpopo province, located at the border of South Africa, Zimbabwe and Botswana), the Cape Floral Kingdom (Western Cape), the Richtersveld Cultural and Botanical Landscape (in the Northern Cape, along the Orange River border with Namibia) and the Vredefort Dome (Free State).
In addition, there are also several heritage sites declared by SAHRA, which include the Castle of Good Hope, the Bushmanskloof Rock Painting Landscape, the Daljosafat Cultural Landscape, the SS Mendi Memorial, the South African Astronomical Observatory, Liliesleaf Farm and the West Coast Fossil Park, among others.

The Business Challenge
“It’s our intention to have a proper electronic document records management system in place so that we can get all our information, including our records and administrative systems, more digital,” explains Muller.
“We are moving forward in this regard; for example we have a YouTube channel and we use it to broadcast on pertinent issues, including a webinar in September – which is Heritage Month in South Africa – which is geared towards allowing the public to share in the conversation. I like to say that even though we’re a heritage organisation, it doesn’t mean that our technology or infrastructure needs to be heritage as well!”
In the quest to keep SAHRA’s digital processes and communications systems modern and not ‘vintage’, the organisation has carried out a significant number of implementations or upgrades in the past 10 years or so. These include such important technology elements as:
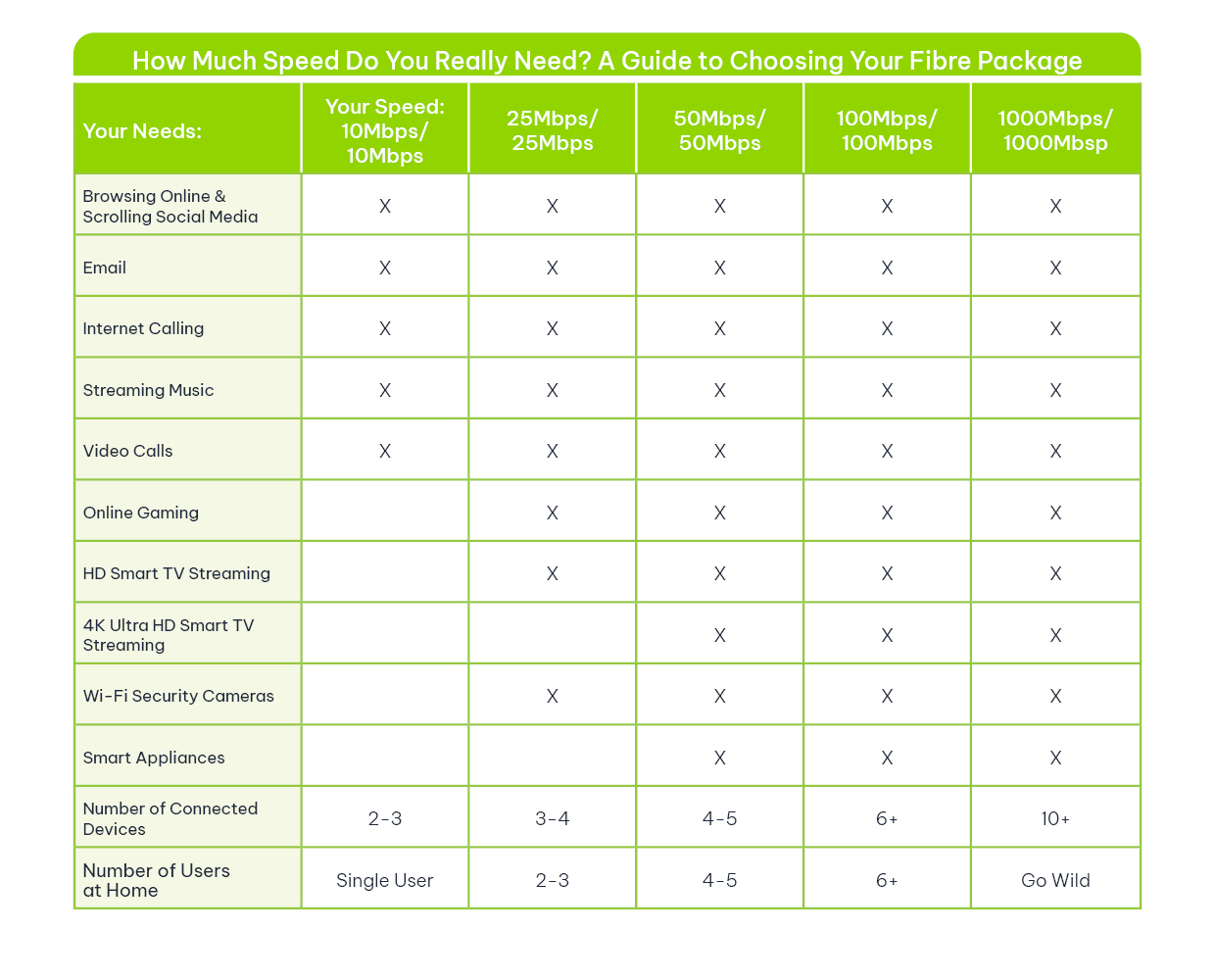
- Business Fibre connectivity;
- Voice and Telephony solutions;
- Backup of data;
- Foundational network security; and
- The implementation of an SD-WAN solution.
Some of these implementations have been carried out at SAHRA’s head office in the Western Cape, and others have been at regional offices. SAHRA operates across four sites around the country. Muller clarifies that there have been some challenges previously with getting all the sites connected with fast connectivity, including the use of a slow ADSL line at one of the regional offices.
“Our concerns were around data security and service continuity, as well as site integrations that were required to interlink all our colleagues and allow them to interact and integrate with our existing systems and offices. Vox was able to address these requirements through well detailed bids,” he explains.
The Business Solution
As a government entity, SAHRA is required to follow strict bidding / tender procedures each time a new project or upgrade over a particular Rand value is required. Muller explains: “Being a government entity, we have to follow a formal public procurement process and that’s always done by a means of competitive bidding. SAHRA’s relationship with Vox began when we had to shift our existing voice solution, and then we also added in the Internet connectivity as well. Later on, we found the need to include managed firewall services and most recently we have had a requirement for an SD-WAN solution.
“On each of these occasions, Vox has submitted separate tender documentation in response to the advertised tenders. In summary, Vox has helped SAHRA to improve on our operational efficiency, including the enhancement of our remote working capabilities. Additionally, Vox has helped us to strengthen our cybersecurity posture, while also reducing infrastructure costs over time.”
Vox was the successful winner of a number of tender processes for SAHRA in recent years, as follows:
2018/2019: Hosted Digital Communication System
- Fibre connectivity
- Verto Hosted PBX and Yealink handsets
- Uncapped Voice
- Communications Manager (TMS)
- Network Cabling
- Chrome Air (Voice over LTE)
- Number porting
2020: Poly Studio VC Solution
2021: Veeam Backup & Replication Enterprise Plus
2022: Connectivity and Voice and Network security
- Primary and failover connectivity at five sites
- Consists of fibre, wireless and LTE
- Moved from Verto Supreme to 3CX Cloud for PBX, Unified Communication and mobility services
- Uncapped Voice
- Fortigate Firewall at five sites
2024: Connectivity and Voice and Network security / SD-WAN
- Provision of two stand-alone internet links at four sites
- Consists of fibre, wireless and LTE
- Moved from Verto Supreme to 3CX Cloud for PBX, Unified Communication and mobility services
- Uncapped Voice
- Fortigate Firewall at five sites with SD-WAN for WAN resiliency
René Minnie, Key Account Manager at Vox, clarifies that the most recent 2024 upgrades are of particular interest and significance for SAHRA, involving upgrades to the entity’s connectivity, voice and network security. She says: “When we look at the migration from Verto Supreme to 3CX Cloud, we see that Vox is providing SAHRA with a solution that is future-proof and rich in functionality, and which allows more control. With regards to the implementation of an SD-WAN solution, it is important to note that Vox has provisioned for the ability to use both links at each site.
“As for the benefits of SD-WAN, it’s a modern networking solution that simplifies the management and operation of a wide area network (WAN) by decoupling the network hardware from its control mechanism, with key benefits including improved network performance, cost efficiency, enhanced security, simplified management, and scalability and flexibility.”
More details on the benefits of SD-WAN are as follows:
- Improved Performance: SD-WAN intelligently routes traffic across the most efficient paths, reducing latency and improving application performance, especially for cloud-based services.
- Cost Efficiency: SD-WAN allows businesses to use lower-cost internet connections (like broadband) alongside or instead of expensive MPLS links, significantly reducing WAN costs.
- Enhanced Security: Built-in encryption, firewall capabilities and centralised security policies help protect data across all network endpoints.
- Simplified Management: Centralised control makes it easier to configure, monitor and manage the network, reducing the need for manual intervention and on-site IT support.
- Scalability and Flexibility: SD-WAN supports rapid deployment across multiple locations and adapts easily to changing business needs, making it ideal for growing organisations.
A Strategic Partner Towards the SAHRA IT Unit
Muller says he has been very happy with both the service and the products received from Vox overall, and enjoys an extremely positive relationship with Vox. He clarifies: “The service levels have always been consistently high, and in fact have always exceeded what we at SAHRA have requested. We also very much appreciate the scalability of the available offerings.
“You could say that Vox has essentially become a strategic partner towards the SAHRA IT unit, and as a company, its employees and divisions are very good at communicating the available offerings, both for a present requirement as well as for future possibilities and planning – I find Vox to be well-structured and transparent.”
Muller also praises the quality of Vox’s tender documents, which, he says, are unfailingly of a high quality and provide all the information – and sometimes more – than actually required.
“Usually, we look to see that the potential service providers are able to meet or even exceed our minimum requirements,” he explains. “Then we look at proven reliability and uptime, scalability, security and compliance. Cost-effectiveness plays a vital role as well, and we also look at strong support and after-sales service.
“Vox scores consistently highly across all these categories, including with excellent service and competitive pricing across all its products. The type of bid received from Vox overall is always excellent. No matter big or small, there’s always enough information. If it’s a specific brand or model mentioned, there will be a specification sheet that paints a clear picture.”
Minnie adds that the interactions with Muller and the rest of his team at SAHRA have always been most pleasant: “As a company, people across a number of divisions at Vox appreciate SAHRA’s business relationship, which is based on mutual politeness and respect. Our two companies work extremely well together, and we look forward to continuing to be of assistance to SAHRA for many years into the future,” she says.
“I believe that in Vox, SAHRA has found an excellent partner and over the years, we have met regularly and enjoyed smooth operations overall. And so if I could sum it up, Vox’s offerings are a clear commitment to a partnership with long-term value overall, because of the scalability and expansions that are offered by Vox,” concludes Muller.
FAQs
What is SD‑WAN and why is it important for heritage institutions?
SD‑WAN is a modern WAN architecture that intelligently routes traffic across multiple links. It improves performance, resilience and security, which is critical for institutions needing reliable access to cloud archives and remote collaboration.
Which Vox products were implemented at SAHRA?
Vox implemented Business Fibre, voice platforms (Verto Hosted PBX historically and migration to 3CX Cloud), Yealink handsets, Fortigate firewalls, Veeam backup and Poly Studio VC, plus wireless/LTE failover.
How does SD‑WAN improve security?
SD‑WAN supports centralised security policies, encryption of WAN links and integration with managed firewalls, reducing exposure for distributed sites and sensitive data.
Can SD‑WAN reduce costs for government agencies?
Yes. By enabling the use of lower‑cost broadband and LTE alongside fibre, SD‑WAN can lower WAN expenses while maintaining performance and resilience.
How did Vox ensure compliance with SAHRA’s procurement rules?
All implementations were awarded through formal competitive tenders, with Vox submitting detailed, compliant bid documents for each procurement phase.
Will SD‑WAN help with disaster recovery and backups?
SD‑WAN improves connectivity resilience which supports replication and backup workflows. Combined with solutions like Veeam, it strengthens overall data protection and recovery capabilities.
Is 3CX Cloud suitable for public sector organisations?
3CX Cloud provides unified communications, mobility and scalability, making it suitable for public sector needs when paired with secure network infrastructure and managed services.
How can heritage organisations begin modernising their IT?
Start with a connectivity assessment, define continuity and security requirements, and procure resilient links, firewall protection and a future‑proof voice platform. Consider a phased tendered approach similar to SAHRA’s.