…with Cybersecurity Measures and Real-time Backups
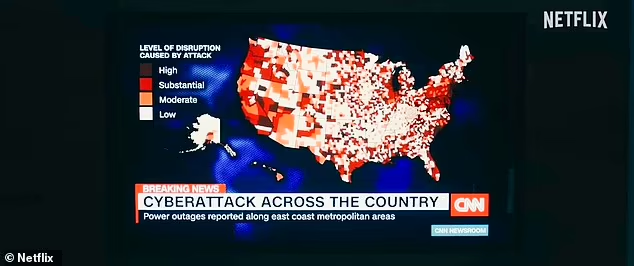
Remember the Transnet cyberattacks of July 2021? They brought huge parts of the country’s supply chains to a standstill for weeks and were a grim reminder of the damage that a cybersecurity breach can cause, not only to a company, but to a country itself. The fact that such a level of disruption can take place at a national level is a stark reminder of how critically important cybersecurity is today, for larger and smaller businesses alike.
Transnet – the nation’s ports, rail and pipelines operator – became a victim of a huge ransomware attack on 22 July 2021, which took offline its IT system, several of its websites and its vital container terminal operating system. Trucks backed up outside Durban harbour on land while ships did the same at sea, as turnaround times to collect or offload containers turned from hours into days because of the manual processes that had to be implemented.
Finally, four days later on 26 July, the company was forced to throw in the towel, and Transnet Port Terminals sent a letter declaring ‘force majeure’ – because of ‘an act of cyberattack, security intrusion and sabotage’ – at several key container terminals, including the Ports of Durban, Ngqura, Port Elizabeth and Cape Town. Under international law, force majeure refers to an irresistible force or unforeseen event beyond the control of a state, making it materially impossible to fulfil an international obligation.

For South African businesses and the country itself, this was a further disaster for the economy, coming on the back of the COVID-19 global pandemic in 2020 and the wave of civil unrest that had taken place in KwaZulu-Natal and Gauteng earlier that month.
We take a closer look at the importance of implementing cybersecurity measures, including real-time back-ups, to help organisations keep their operations running during major disruptions.
Like the Boy Scouts Always Said: ‘Be Prepared!’
Whether it’s a cyberattack, natural disaster, system failure or even human error, organisations must always be prepared to respond and recover, fast. A business that isn’t prepared will risk prolonged downtime, financial losses and reputational damage – all of which happened in the Transnet cyberattack
Cybersecurity measures will help to protect against attacks before they can happen, using immutable backups as well as secure vaults to recover from ransomware. Real-time backups and replication use technologies to ensure minimal data loss.
The benefits of enhanced business resilience include minimising downtime and thus preventing financial losses; protecting your business’s reputation, which helps to maintain customer confidence and ensure future customers; and meeting regulatory compliance requirements, both legal and industry-specific.
Unexpected disruptions can bring businesses to a standstill at any time, with no warning. While global pandemics and civil unrest obviously remain out of the control of business, implementing effective cybersecurity measures, including real-time backups, can keep businesses of all sizes still running during major disruptions.
Organisations that fail to implement these measures face severe risks. We just have to think back to late July 2021 to be reminded of the importance being able to keep operations running during cyberattacks – for businesses of all sizes. ‘Too big to fail’ is not an effective security strategy.
Vox offers cybersecurity solutions to assist our business clients in protecting their systems and processes, and their data – click here to find out more about our offerings.
Frequently Asked Questions
What are real‑time backups and how do they keep operations running during a cyberattack?
Real‑time backups capture and replicate data continuously or at very short intervals so the most recent data is available for recovery. During a cyberattack—especially ransomware—real‑time backups reduce data loss and speed up recovery, helping operations resume faster. For managed real‑time replication, speak to Vox about our Real‑time Backup & Replication solutions.
How do immutable backups protect against ransomware?
Immutable backups are write‑once, read‑many copies that cannot be altered or deleted by attackers, ensuring a clean copy of your data is always available for restoration. Pairing immutable backups with secure vaulting is a best practice for resilient ransomware recovery—Vox’s Immutable Backup Vaults can be configured to meet regulatory and business requirements.
Are backups alone enough to ensure business continuity?
Backups are essential but not sufficient alone. Effective business continuity combines preventive cybersecurity measures (patching, endpoint protection, network security), incident response plans, and tested disaster recovery procedures alongside backups.
Are real‑time backups suitable for small and medium enterprises in South Africa?
Yes. SMEs benefit from real‑time replication and managed backup services because they minimise data loss and avoid prolonged downtime without the need for large in‑house teams. Vox offers scalable backup and managed security services tailored to SME budgets and compliance needs.
What is a secure vault and why is it important for backup strategy?
A secure vault is an isolated, protected storage location, often with immutability and strict access controls, designed to keep backup copies safe from unauthorised changes or deletions. Secure vaulting prevents attackers from destroying backups as part of an attack; Vox’s Secure Backup Vault solutions provide controlled retention and strong access policies.