Meet our Experts: Spotlight on Michelle du Plessis
At Vox, we value, support and actively engage people with the levels of expertise that we require to keep us moving forward as a company. In this edition of ‘Meet our Experts’, we find out more about Michelle du Plessis, who works for Vox Weather as a Meteorologist. She plays a key role in bringing local audiences our vital, regular weather forecasts.
Michelle regards meteorology as being a balance and blend of science and storytelling. And certainly it’s come a long way, from ancient civilisations observing celestial patterns or monitoring the movements of birds and animals, to the modern-day usage of advanced technology and complicated maths.
Michelle – who is one half of the acclaimed Vox Weather duo, together with colleague and mentor Annette Botha – shares details about her daily working life, as well as some of her challenges and aspirations.
We also find out more on how hard she has worked to follow her dream.
Inspiration During High School
Michelle’s future career as a meteorologist began in high school, where she loved Geography and was also good at Maths. She explains: “My Geography teacher, Mrs Esther Fourie, was simply amazing and truly inspirational. I became interested in pursuing Geography at the tertiary education level, but I wasn’t too sure initially of what was available to me in the field.”
Here she smiles: “I wasn’t that keen on looking at rocks, for instance! But I really liked the weather component of Geography. So I did some research and decided to study meteorology. Once at university, I found the course to be very scientific and also mathematical, and in fact more challenging than I’d expected, but always very enjoyable.”
Michelle studied for a BSc Meteorology at the University of Pretoria, which is currently the only university in South Africa to offer the course, and she then went on to complete her Honours degree, graduating Cum Laude and at the top of her class. It wasn’t always plain sailing though: financial and COVID-linked challenges were looming.
Grit and Determination
Having been granted a bursary during her undergraduate years, Michelle had to start paying for her studies in full during her final Honours year. “It was financially challenging,” she says, “but I managed to get through by juggling a couple of jobs while I was still studying. I found different work for myself, doing a bookkeeping job as well as some tutoring work. Fortunately, I do like both Maths AND children – if I hadn’t become a meteorologist I could easily have become a teacher!”
Another significant challenge came about because of the COVID-19 pandemic. Michelle explains: “I was doing my Honours degree during the COVID period, and it ultimately had a very negative impact on job opportunities in the broader meteorology arena. This was largely because most graduate meteorologists would traditionally be absorbed by the South African Weather Service (SAWS) after they had finished their studies.
“However, one of the main incomes for SAWS is the production of forecasts relating to the aviation industry, and obviously COVID caused global flights to be cut back severely. The end result was that, in the year after I’d finished my Honours degree, SAWS wasn’t able to hire in any of the meteorology graduates from my year, which was a serious blow for all of us at the time.”
However, Michelle is both determined and resourceful, and so to support herself, she continued with her previous bookkeeping and tutoring jobs for about another year or so – something which, she says, taught her continued resilience and perseverance, even while her dream job wasn’t immediately within reach.
“I definitely had some tough moments along the way,” she admits, “but I also learned that hard work and staying positive can eventually pay off. I don’t like dwelling too much on the past – I believe that everyone faces their own challenges.”
Her chance to finally work in her chosen field came when she was able to join Annette at Vox Weather from February 2023 as a Junior Meteorologist.
“It’s really fulfilling to be working today in the field that I studied for,” she says. “I’m so grateful for the opportunity to be working now as a meteorologist and gaining exposure to a truly interesting and satisfying working life.”
It’s also clear that her formative challenges have helped to shape her impressive work ethic.
A Day in the Life…
So what does a day in the life of a meteorologist look like?
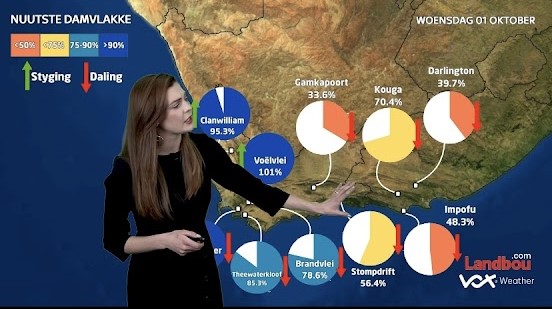
Michelle says a typical week involves analysing weather models and trends, preparing the daily forecasts, and switching into content creation and filming to produce material across different platforms, from short TikTok clips to the main daily show that goes live at 18:00. In short, forecasting requires scientific modelling work, after which content must be created for different audiences and formats.
She explains: “Basically I forecast and present the weather, but that’s not all. We also do quite a lot of interviews with newspapers and radio stations. Then besides that, we additionally plan field trips, including for our ‘Beyond the Forecast’ episodes, where we go a bit deeper into how weather can impact on other experiences. So it’s a lot of science, and then quite a bit of fun as well!”
Her field work is an important and much‑loved part of the job, including snow chases, Namaqualand flower shoots, and even hot‑air balloon and paragliding experiences – all in the name of finding out more about the local weather and its effects.
Says Michelle: “So much of my field work has already become what you could call ‘bucket list’ types of experiences. Having grown up in Pretoria and then relocated to the Western Cape for Vox Weather, I hadn’t previously experienced snow until we went snow chasing for work last year, which was amazing and today is one of my favourite memories!”
And staying with the idea of ‘snow angels’, Michelle adds that she “likes to think of the Vox Weather meteorologists as being South Africa’s Weather Fairies…!”
It’s a fun thought, because fairies traditionally help to make good things happen, and Michelle and Annette together do just that, using modern technology for both the initial weather forecasting as well as sharing their information and analyses via the Internet.
When discussing the audience differences across various social media platforms, Michelle notes that TikTok attracts a younger audience, while Facebook often brings older and more seasoned followers.
“Geographically, Vox Weather’s biggest engagement comes from the major urban centres, including Gauteng, Cape Town, Durban, Port Elizabeth and Bloemfontein,” she outlines, “while the audience engagement can also vary by season and region. For example, people in Gauteng often react strongly to cold snaps and hail, while Western Cape viewers are more used to rain and winter patterns.
“In general though, it’s safe to say that engagement tends to spike during extreme or unusual weather events. Our Vox Weather community is overwhelmingly positive and appreciative, with only the odd negative comment that we don’t dwell on.”
Challenges and Resilience
Being in the public eye can be challenging,” Michelle confirms, “and there are obviously times when we get negative comments – we do sometimes get the forecast wrong! People can be quite harsh on us if we predicted rain that then didn’t happen, for example.
“My response then is to ask people to remember that the atmosphere overall is quite complex, and that a small change can make a big difference. We always say: ‘It’s just the forecast – it’s not a promise!”
She notes that another challenge includes presenting in English, which isn’t her home language (Michelle comes from an Afrikaans upbringing originally), but she continues working on her linguistic skills.
To counteract these occasional work challenges, Michelle is grateful that the team at Vox Weather is friendly and supportive, with Annette being a kind and flexible mentor: “I’ve been allowed to work with a significant amount of creative and professional freedom while developing my own presentation style, wardrobe choices and the planning of shoots,” she says.
“I also have tremendous support from my husband, Renaldo, and I’m really enjoying married life – I’m finding it an absolute joy. I’m so lucky to be married to someone who supports me wholeheartedly – he’s my calm in the chaos! While I do miss some key family members and friends, moving to Cape Town together has opened up a meaningful new chapter for us.”
Into the future, Michelle would like to continue with her academic studies at some point by doing a master’s degree, possibly with a focus on changes to rainfall patterns under a warming climate. She’s also interested in growing further within Vox Weather and having her own future role in mentoring other meteorologists going forward.
“I’m very proud to be part of Vox Weather,” says Michelle. “We’ve built a brand that people trust, and we’ve worked really hard to get there. I also love the fact that every day is different, whether we’re forecasting and standing in front of the camera, or out in the field.
“I’m very grateful for the job I have, and I love every day of it. And just know, when you see me on the screen having fun during a snow chase, that it probably took three weather models, two coffees and one very determined fellow meteorologist to get me there!” she concludes.